Lab 13 – Threat Hunting Fundamentals
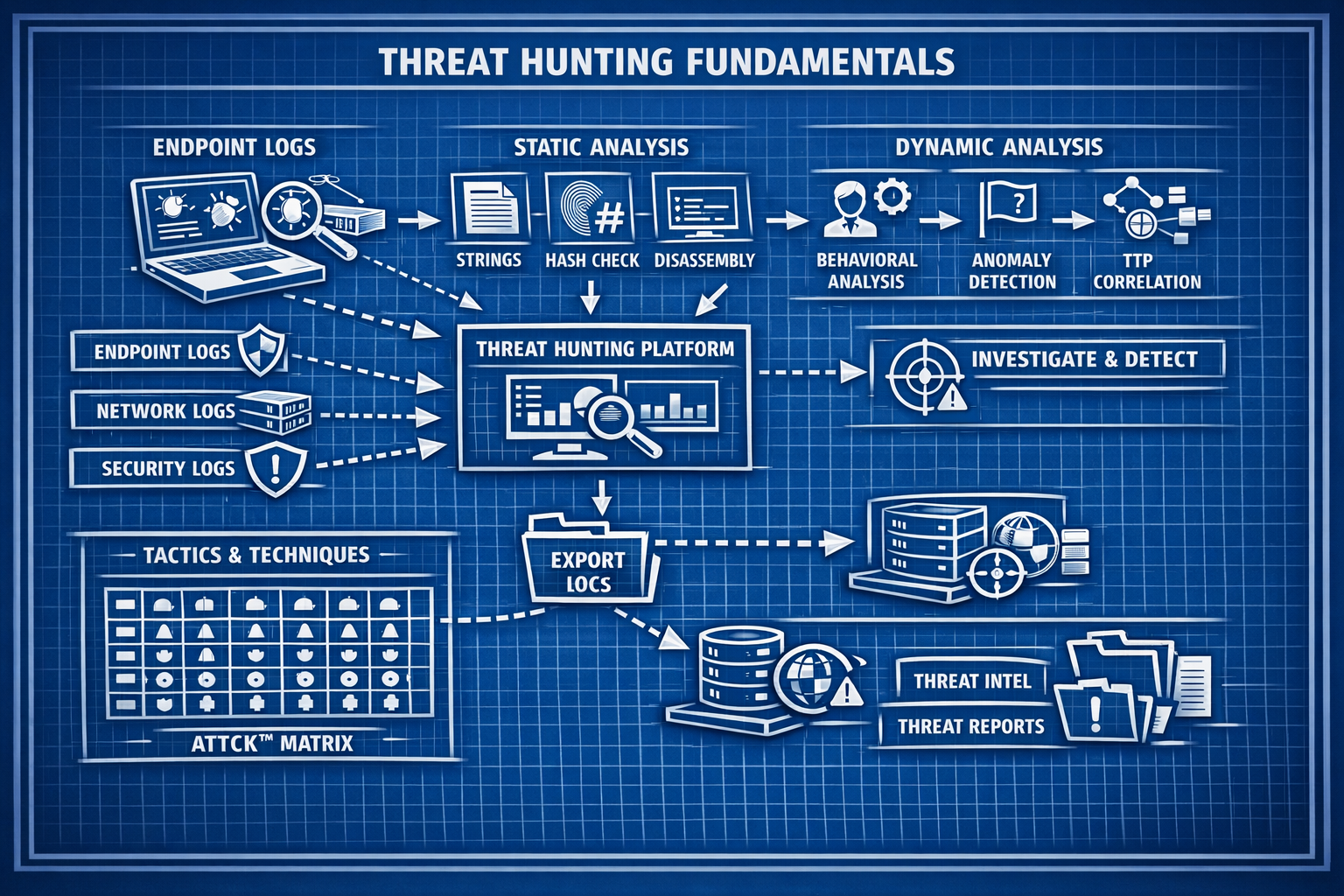
Learn structured threat‑hunting methodology, build your first hunting queries, and create a repeatable workflow for proactive detection.
Objective Lab goal
This lab introduces the fundamentals of threat hunting: hypothesis‑driven investigation, structured queries, and repeatable workflows. You’ll build your first hunting playbook and run hunts across authentication, system, and network logs.
- Outcome 1: Understand the threat‑hunting lifecycle.
- Outcome 2: Build hypothesis‑driven hunting queries.
- Outcome 3: Create a repeatable hunting workflow.
- Outcome 4: Document findings and next steps.
Lab 13: Building structured threat‑hunting workflows and hypothesis‑driven queries.
Deliverables End‑of‑lab checklist
- DL13.1: Documented hunting workflow.
- DL13.2: Three hunting hypotheses created.
- DL13.3: Hunting queries executed in SIEM.
- DL13.4: Findings documented with screenshots.
- DL13.5: Next‑step improvements identified.
Lab Steps Step‑by‑step instructions
Step 1 – Learn the Threat‑Hunting Lifecycle
~20 minutes- Review the four stages:
- Hypothesis creation
- Data collection
- Investigation
- Documentation & feedback
- Identify which SIEM dashboards support each stage.
Step 2 – Create Hunting Hypotheses
~45 minutes- Create three hypotheses, such as:
- “A compromised account is performing unusual authentication attempts.”
- “A host is making suspicious outbound DNS queries.”
- “A workstation is scanning internal network ranges.”
- Map each hypothesis to relevant log sources.
Step 3 – Build Hunting Queries
~60 minutes- Use your SIEM query language to build structured hunts:
- Failed logon spikes
- Unusual DNS domains
- High‑volume network connections
- Save queries for reuse in future hunts.
Step 4 – Document Findings & Build Workflow
~45 minutes- Create a hunting workflow including:
- Hypothesis
- Data sources
- Query
- Findings
- Next steps
- Document findings with screenshots.
- Identify improvements for future hunts.
Reflection What you should understand now
- Methodology: How structured hunting improves detection.
- Queries: How to build hypothesis‑driven searches.
- Workflow: How repeatable processes accelerate investigations.
With your first hunting workflows complete, you’re ready to automate enrichment and response in Week 14.