Month 4 – Threat Hunting & Automation
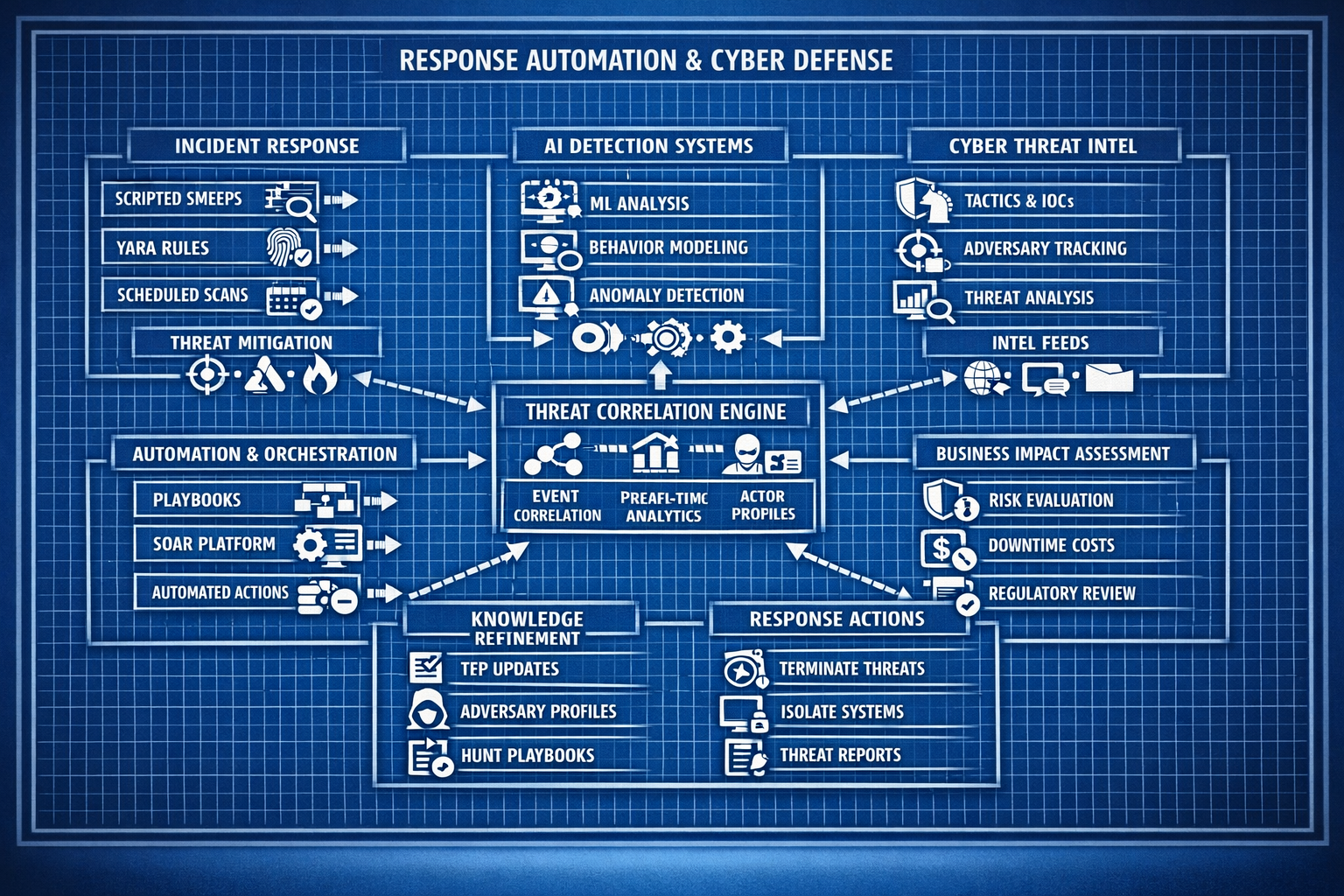
Build proactive detection capabilities through structured threat‑hunting workflows, automated enrichment, and response playbooks.
Overview What you will accomplish
Month 4 focuses on proactive defense. You’ll build repeatable threat‑hunting workflows, automate enrichment and response tasks, and create dashboards and playbooks that accelerate investigations.
- Develop structured threat‑hunting queries and workflows.
- Automate enrichment using scripts, APIs, and SIEM features.
- Create response playbooks for common attack patterns.
- Build dashboards that support hunting and triage.
- Simulate attacker behavior to validate hunting logic.
Labs Week‑by‑week breakdown
Week 13 – Threat Hunting Fundamentals
Learn structured hunting methodology, build your first hunting queries, and create a repeatable workflow for investigations.
Week 14 – Automated Enrichment & Scripting
Use APIs, scripts, and SIEM automation features to enrich alerts with context from threat‑intel, DNS, and system logs.
Week 15 – Response Playbooks & Workflow Design
Build structured response playbooks for brute‑force attacks, malware alerts, suspicious DNS activity, and lateral movement.
Week 16 – Threat Hunting Validation & Attack Simulation
Simulate attacker behavior and validate your hunting queries, dashboards, and playbooks against real‑world patterns.