Month 5 – Endpoint Security & EDR
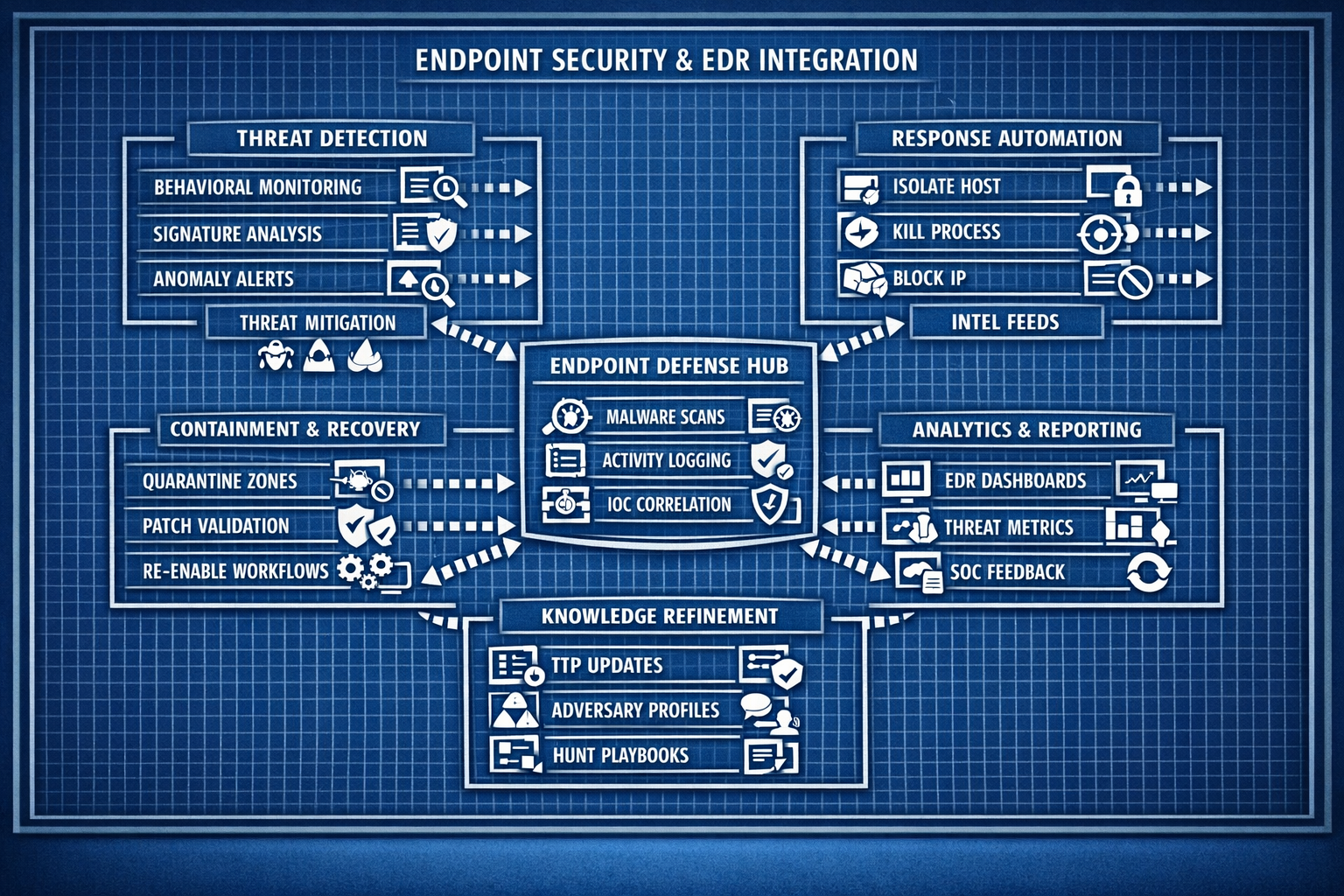
Deploy modern endpoint‑detection tooling, analyze host‑level telemetry, and build response workflows for malware, persistence, and lateral movement.
Overview What you will accomplish
Month 5 focuses on endpoint‑level visibility and detection. You’ll deploy EDR tooling, analyze host telemetry, detect suspicious processes, and build response workflows for malware, persistence, and lateral movement.
- Deploy EDR agents across your homelab endpoints.
- Analyze host telemetry including processes, services, registry, and network activity.
- Detect malware behavior, persistence mechanisms, and privilege escalation attempts.
- Build endpoint‑focused response workflows and automation.
- Simulate endpoint attacks to validate detection and response.
Labs Week‑by‑week breakdown
Week 17 – EDR Deployment & Host Telemetry
Deploy EDR agents to your Windows and Linux endpoints, validate telemetry ingestion, and explore process, service, and network‑activity visibility.
Week 18 – Malware Behavior & Process Analysis
Analyze suspicious processes, command‑line activity, and malware‑like behavior using EDR telemetry and sandbox‑style simulations.
Week 19 – Persistence, Privilege Escalation & Lateral Movement
Detect persistence mechanisms, privilege‑escalation attempts, and lateral‑movement behavior using host‑level logs and EDR alerts.
Week 20 – Endpoint Response Automation & Playbooks
Build automated response workflows for malware alerts, suspicious processes, and compromised accounts using EDR and SIEM integration.