Lab 19 – Persistence, Privilege Escalation & Lateral Movement
Detect persistence mechanisms, privilege‑escalation attempts, and lateral‑movement behavior using EDR telemetry and host‑level logs.
Objective Lab goal
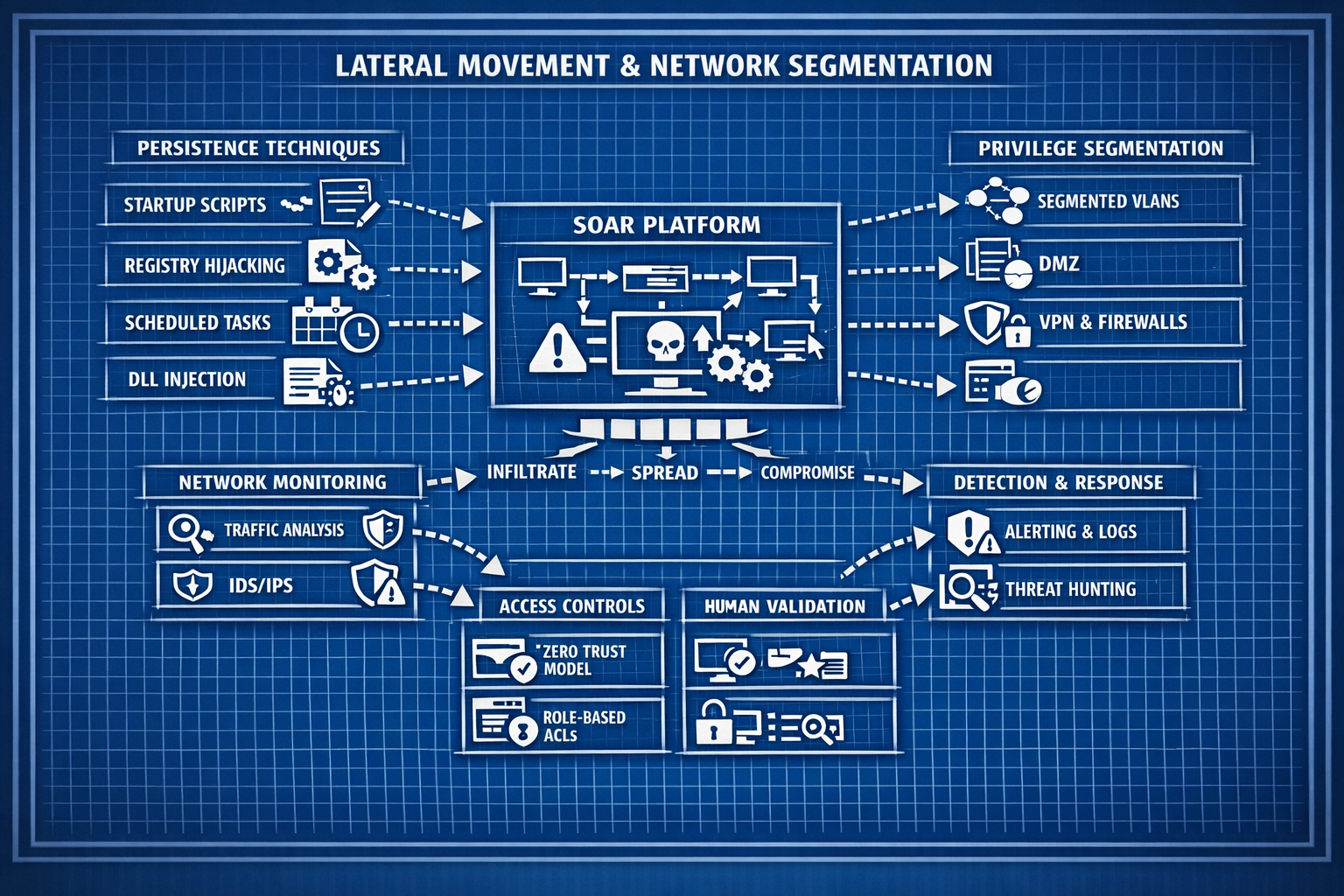
This lab focuses on detecting attacker techniques that occur after initial compromise. You’ll simulate persistence creation, privilege‑escalation attempts, and lateral movement, then validate that your EDR and SIEM correctly detect and correlate these behaviors.
- Outcome 1: Persistence mechanisms created and detected.
- Outcome 2: Privilege‑escalation attempts simulated and analyzed.
- Outcome 3: Lateral‑movement behavior detected using host and network telemetry.
- Outcome 4: MITRE ATT&CK mapping completed for all behaviors.
Lab 19: Detecting persistence, privilege escalation, and lateral movement using EDR telemetry.
Deliverables End‑of‑lab checklist
- DL19.1: Persistence mechanism created and detected.
- DL19.2: Privilege‑escalation attempt simulated and logged.
- DL19.3: Lateral‑movement behavior detected.
- DL19.4: MITRE ATT&CK mapping completed.
- DL19.5: Documentation updated with screenshots and findings.
Lab Steps Step‑by‑step instructions
Step 1 – Simulate Persistence Mechanisms
~60 minutes- Create benign persistence mechanisms:
- Registry Run key
- Scheduled task
- Startup folder script
- Observe EDR alerts for:
- Registry modification
- Task creation
- New startup items
- Document findings and baseline patterns.
Step 2 – Simulate Privilege‑Escalation Attempts
~45 minutes- Trigger benign privilege‑escalation patterns:
- runas /user:Administrator cmd.exe
- Attempt to modify protected registry keys
- Attempt to start/stop system services
- Observe EDR telemetry for:
- Access denied events
- Token manipulation attempts
- Service‑control activity
- Document findings with screenshots.
Step 3 – Simulate Lateral Movement
~60 minutes- From WIN10‑LAB, attempt:
- psexec \\DC01 cmd.exe
- wmic /node:DC01 process call create
- SMB share enumeration
- Observe EDR telemetry for:
- Remote service creation
- Remote process execution
- Unusual authentication patterns
- Correlate with SIEM logs.
Step 4 – Map Findings to MITRE ATT&CK
~30 minutes- Map behaviors to ATT&CK techniques:
- T1053 – Scheduled Task
- T1547 – Registry Run Key
- T1068 – Privilege Escalation
- T1021 – Remote Services
- T1075 – Pass‑the‑Hash (if simulated)
- Document mappings in your lab notes.
Reflection What you should understand now
- Persistence: How attackers maintain access after compromise.
- Privilege escalation: How attackers gain higher permissions.
- Lateral movement: How attackers pivot across systems.
With these behaviors analyzed, you’re ready to automate endpoint response workflows in Week 20.