Lab 20 – Endpoint Response Automation & Playbooks
Build automated response workflows for malware alerts, suspicious processes, and compromised accounts using EDR and SIEM integration.
Objective Lab goal
This lab focuses on automating endpoint‑response actions using your EDR and SIEM platforms. You’ll build workflows that isolate hosts, kill malicious processes, enrich alerts, and notify administrators automatically.
- Outcome 1: Automated response workflows created.
- Outcome 2: EDR actions integrated with SIEM automation.
- Outcome 3: Alerts enriched and escalated automatically.
- Outcome 4: Playbooks validated using simulated attacks.
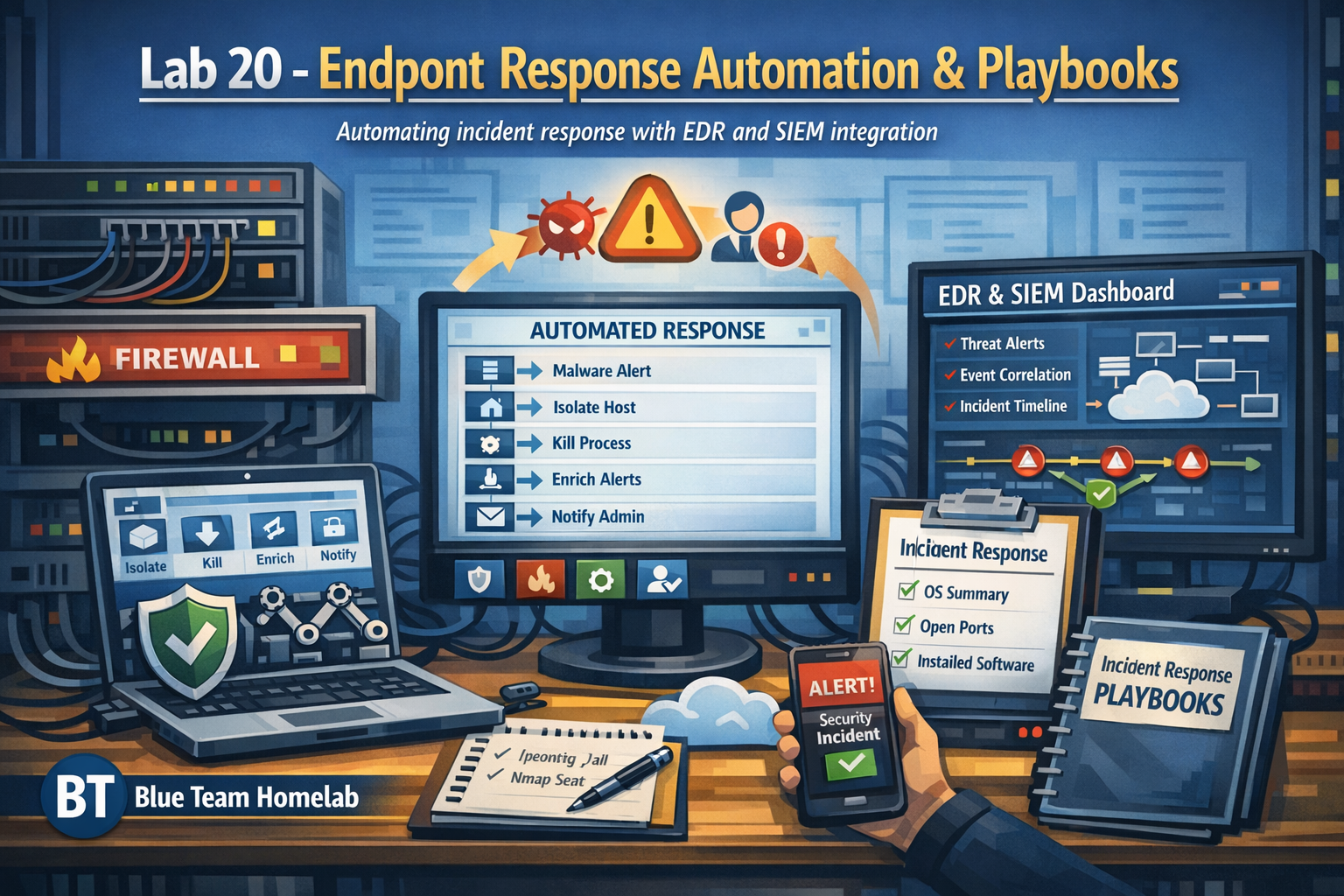
Lab 20: Automating endpoint response workflows using EDR and SIEM integration.
Deliverables End‑of‑lab checklist
- DL20.1: Automated malware‑response workflow.
- DL20.2: Automated suspicious‑process workflow.
- DL20.3: Automated compromised‑account workflow.
- DL20.4: EDR + SIEM integration validated.
- DL20.5: Documentation updated with workflow diagrams.
Lab Steps Step‑by‑step instructions
Step 1 – Build Malware‑Response Automation
~60 minutes- Create a workflow that triggers on:
- High‑severity malware alerts
- Suspicious process behavior
- Automate actions:
- Isolate host
- Kill malicious process
- Collect forensic logs
- Send notification to admin.
Step 2 – Automate Suspicious‑Process Response
~45 minutes- Create a workflow that triggers on:
- Encoded PowerShell commands
- Unexpected parent/child process chains
- Automate:
- Process termination
- Hash lookup via threat‑intel APIs
- Alert enrichment
Step 3 – Automate Compromised‑Account Response
~45 minutes- Create a workflow that triggers on:
- Failed logon spikes
- Password‑spray patterns
- Unusual logon hours
- Automate:
- Disable account
- Block source IP
- Notify admin
Step 4 – Validate Workflows with Simulated Attacks
~45 minutes- Simulate:
- Malware‑like process behavior
- Suspicious PowerShell commands
- Failed logon bursts
- Verify:
- Workflow triggers
- Automated actions
- Alert enrichment
- Notifications
- Document results and detection gaps.
Reflection What you should understand now
- Automation: How automated workflows accelerate response.
- Integration: How EDR and SIEM combine to improve detection.
- Consistency: How playbooks reduce human error.
With this lab, you’ve completed Month 5 and built strong endpoint‑response capabilities. In Month 6, you’ll move into cloud security and identity‑focused detection.